How to Choose a Kubernetes Gateway API Implementation
From Understanding Gateway API to Choosing the Right Kubernetes Implementation
In the previous article, we discussed the creeping limitations of Ingress, the structural promise of Gateway API, and the conceptual shift from a single monolithic controller to a well-defined separation of concerns. If you’ve followed that reasoning, you now understand why Gateway API exists and what it’s trying to solve.
But understanding the specification is only the beginning.
Gateway API gives you structure. It does not give you answers. Just like Ingress, it relies on controllers to turn those definitions into real traffic behavior.
The moment you move from “should I adopt Gateway API?” to “which implementation should I deploy?”, you enter territory the spec deliberately leaves open. And that openness, which is genuinely one of Gateway API’s strengths, is also where teams make decisions they’ll be living with for years.
Why Choosing a Gateway API Implementation Is Harder Than It Looks
There’s a trap that catches even experienced platform teams. Because Gateway API is a standard, it’s tempting to treat the choice of controller as an afterthought, an implementation detail you can swap out later if you need to. This assumption is usually wrong because Gateway API implementations vary in:
- How closely they follow the specification
- How they extend beyond it
- Their operational model and maturity
- Their alignment with broader ecosystems (Envoy, NGINX, service mesh, cloud providers)
If you’re not careful, you can recreate the same fragmentation and hidden complexity that made Ingress painful—just with better APIs.
Migrating from Ingress to Gateway API is not just a replacement. It’s an opportunity to reset how traffic is managed in your platform. And that makes the choice of implementation far more consequential than it might initially appear.
How to Choose a Kubernetes Gateway API Controller (Key Criteria)
Before looking at specific implementations, it’s worth defining what matters.
This is not about finding the controller with the most features. It’s about understanding which trade-offs best fit your platform.
In practice, most teams end up evaluating implementations along a few key dimensions:
1. Alignment with Gateway API
- Is Gateway API the primary configuration model?
- Or is it layered alongside existing, implementation-specific APIs?
A tighter alignment usually means better portability and a more future-proof design.
2. Operational model and complexity
- Does it follow a clear control plane / data plane separation?
- How complex is it to deploy, upgrade, and operate?
- What does day-two maintenance look like?
Some solutions optimize for simplicity. Others trade simplicity for flexibility and power.
3. Scope: gateway vs platform
- Is it focused purely on north-south traffic?
- Or does it extend into service mesh and east-west concerns?
A broader scope can be powerful—but it also increases operational overhead.
4. Extensibility and lock-in
- How are advanced features exposed?
- Through standardized APIs or implementation-specific extensions?
Extensions are often necessary—but they can reduce portability if overused.
5. Security and policy model
- Are security features first-class and integrated?
- Or do they depend on external systems or commercial add-ons?
This becomes critical in multi-team or regulated environments.
6. Governance and ecosystem maturity
- Is the project community-driven or vendor-led?
- How mature and widely adopted is it?
This influences long-term stability, support, and evolution.
These criteria reflect real trade-offs that affect how platforms behave under scale, how teams collaborate, and how easily systems evolve over time.
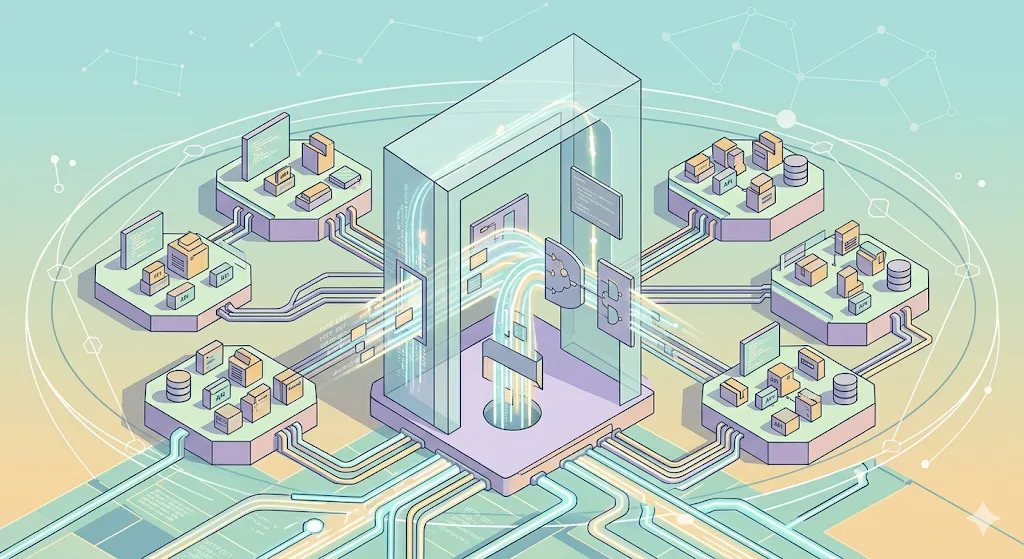
Gateway API Implementations Compared: Envoy, Istio, NGINX, Traefik, and KGateway
With that lens in place, the differences between implementations become easier to reason about.
Each one is not just a tool, but a set of design decisions about how traffic management should work and who owns that complexity.
Envoy Gateway
Alignment with Gateway API
Envoy Gateway shows strong alignment with Gateway API as its primary configuration model. It supports core resources (Gateway, HTTPRoute, GRPCRoute) as well as experimental ones (TCPRoute, UDPRoute, TLSRoute) and tracks the evolution of the spec closely, even if not always immediately on the latest version.
Operational model and complexity
It follows a clear control plane / data plane architecture. The controller translates Gateway API resources into Envoy Proxy’s xDS configuration and manages Envoy Proxy instances. This model is well understood and scalable, though it introduces moderate operational overhead.
Scope: gateway vs platform
Primarily focused on north-south traffic, but integrates naturally into broader ecosystems (API gateways, service mesh, observability stacks) thanks to Envoy.
Extensibility
Provides a structured extension model through CRDs such as BackendTrafficPolicy, ClientTrafficPolicy, and SecurityPolicy. These extend beyond the core spec while maintaining conceptual alignment with it.
Security
Strong and comprehensive: JWT, mTLS, API keys, Basic Auth, OIDC, CORS, and external authorization. Many capabilities are inherited from Envoy’s mature data plane.
Governance
Open source (Apache 2.0), part of the Envoy ecosystem, with strong ties to a CNCF graduated project. Backed by a mature community and governance structure.
Trade-offs
- Strong spec alignment and flexibility
- Mature, high-performance data plane
- Extensions reduce portability across controllers
- Moderate operational complexity
Istio
Alignment with Gateway API
High and improving. Istio supports Gateway API and is moving toward making it the default, but still maintains its own CRDs for advanced features not yet covered by the spec.
Operational model and complexity
High complexity. Uses a full control plane (istiod) and distributed Envoy proxies. Designed for dynamic configuration and large-scale environments, but requires significant operational investment.
Scope: gateway vs platform
Covers both north-south (gateway) and east-west (service mesh) traffic. The broadest scope among all implementations.
Extensibility
Extensible via WebAssembly (Wasm), though this is still evolving and not fully mature. Also relies on its own CRDs for advanced capabilities.
Security
Strong overall, especially in mesh scenarios (mTLS, policy enforcement). For ingress-specific use cases, capabilities are solid but less extensive compared to dedicated gateway solutions.
Governance
Open source (Apache 2.0), CNCF graduated project with high adoption and well-established governance.
Trade-offs
- Unified model for gateway + mesh
- Very powerful but operationally heavy
- Gateway API is not the only configuration interface
- Higher learning curve and maintenance cost
NGINX Gateway Fabric
Alignment with Gateway API
High. Supports standard and experimental resources with a steady update cadence and clear roadmap.
Operational model and complexity
Traditional controller + proxy model. Familiar and predictable, especially for teams already using NGINX. Complexity increases when using NGINX Plus features.
Scope: gateway vs platform
Focused on north-south traffic, with stronger value when integrated into the broader NGINX ecosystem.
Extensibility
Provides multiple implementation-specific extensions (RateLimitPolicy, AuthenticationFilter, SnippetsPolicy, etc.), enabling detailed proxy configuration but tightly coupled to NGINX behavior.
Security
Moderate. Supports basic authentication and mTLS, with more advanced capabilities available through NGINX Plus.
Governance
Open source (Apache 2.0), but closely tied to the NGINX/F5 ecosystem, with less neutral, community-driven governance.
Trade-offs
- Strong ecosystem continuity for NGINX users
- Flexible but tightly coupled extensions
- Advanced features may require commercial offering
- Less neutrality in governance
Traefik Proxy
Alignment with Gateway API
High. Supports Gateway API resources and tracks the spec reasonably well.
Operational model and complexity
Simplified model where the proxy itself acts as both control and data plane. Easier to deploy and operate, with fewer moving parts.
Scope: gateway vs platform
Primarily north-south traffic, with mesh capabilities existing outside the core OSS proxy.
Extensibility
Limited in the open source version. Many advanced features depend on the broader Traefik ecosystem (e.g., Traefik Hub).
Security
Limited in OSS. More advanced features (JWT, OIDC, WAF) are part of the commercial offering.
Governance
Open source (MIT), but primarily driven by Traefik Labs.
Trade-offs
- Very easy to operate and adopt
- Lower feature depth in OSS
- Reliance on commercial ecosystem for advanced capabilities
- Less flexibility for complex scenarios
KGateway
Alignment with Gateway API
Medium-high. Supports most resources but evolves more slowly alongside the specification.
Operational model and complexity
Control plane model similar to Envoy Gateway. May require additional components (e.g., Istio) for certain capabilities like mTLS, increasing complexity in some scenarios.
Scope: gateway vs platform
Focused on north-south traffic, with additional specialization for AI and microservices workloads via agentgateway. Not a full service mesh.
Extensibility
Provides its own CRDs (TrafficPolicy, HTTPListenerPolicy, DirectResponse) to extend functionality, particularly around traffic control and resilience.
Security
Moderate. Covers common needs (CORS, CSRF, access logging), with mTLS often relying on external systems like Istio.
Governance
Open source (Apache 2.0), CNCF Sandbox project. Earlier-stage maturity despite a longer history (formerly Gloo, created by Solo.io).
Trade-offs
- Strong fit for specialized (especially AI-driven) use cases
- Less mature and slower-moving than alternatives
- Some overlap with evolving Gateway API features
- May require complementary tooling for full capabilities
| Implementation | Alignment with Gateway API | Operational Model & Complexity | Scope (Gateway vs Platform) | Extensibility | Security | Governance | Trade-offs |
|---|---|---|---|---|---|---|---|
| Envoy Gateway | Strong alignment, spec-first model. Supports core (Gateway, HTTPRoute, GRPCRoute) and experimental (TCPRoute, UDPRoute, TLSRoute) resources. Tracks spec closely. | Clear control plane / data plane. Translates Gateway API → Envoy xDS. Scalable but moderate operational overhead. | Gateway-focused (north-south), integrates well with mesh and observability ecosystems. | Structured CRDs (BackendTrafficPolicy, ClientTrafficPolicy, SecurityPolicy) aligned with spec philosophy. |
| OSS (Apache 2.0), part of Envoy ecosystem, CNCF-aligned, mature governance. |
|
| Istio | High and improving. Gateway API supported but coexists with Istio CRDs. | High complexity. Full control plane (istiod) + distributed proxies. Significant operational investment. | Gateway + Mesh (north-south + east-west). Broadest scope. |
|
| OSS (Apache 2.0), CNCF Graduated, highly mature. |
|
| NGINX Gateway Fabric | High. Supports standard and experimental resources with steady updates. | Controller + proxy model. Familiar, complexity increases with NGINX Plus. | Gateway-focused (north-south), strong fit within NGINX ecosystem. |
|
| OSS (Apache 2.0), but closely tied to NGINX/F5. |
|
| Traefik Proxy | High. Solid Gateway API adoption. | Simplified: proxy acts as control + data plane. Low operational overhead. | Gateway-focused (north-south). Mesh outside core OSS offering. | Limited in OSS. Advanced features tied to broader ecosystem (e.g., Traefik Hub). |
| OSS (MIT), vendor-led by Traefik Labs. |
|
| KGateway | Medium-high. Supports most resources but evolves more slowly. | Control plane model similar to Envoy. May require Istio for some capabilities. | Gateway-focused (north-south) with specialization in AI/microservices. |
|
| OSS (Apache 2.0), CNCF Sandbox, emerging maturity. |
|
How to Choose the Right Gateway API Implementation for Your Platform
Based on real-world platform engineering experience, here is how we’d reason through the decision:
- If your primary goal is replacing Ingress with something that’s genuinely designed around Gateway API’s model, Envoy Gateway is the most coherent choice. Its extension model, security depth, and alignment with the spec’s evolution make it the strongest general-purpose option for most platform teams. You’re not betting on a controller that bolted on Gateway API support, you’re adopting one that was built around it.
- If you need to unify ingress and service mesh under a single platform, Istio is the only option that credibly addresses both. This is the right call when internal service-to-service complexity has reached the point where a mesh is genuinely warranted — not as a hedge, but as a response to a clear operational need. If you’re not yet at that point, defer this decision. Don’t buy mesh complexity to solve an ingress problem.
- If your organization has deep operational investment in NGINX and continuity matters more than feature breadth, NGINX Gateway Fabric is a pragmatic choice. You’ll trade some security depth and governance neutrality for a smoother operational transition. For teams where that trade-off is acceptable, it’s defensible.
- If you’re operating a smaller platform and want to minimize moving parts, Traefik Proxy’s simpler architecture has real appeal. Go in with clear eyes about where the commercial tier begins, and make sure your projected security and extensibility requirements don’t outpace what the OSS proxy provides.
- If AI workloads are a first-class concern for your platform, KGateway deserves evaluation that the other controllers don’t need. The capabilities it adds for LLM routing and agent-oriented infrastructure are unique. Accept the trade-off on security depth and spec cadence, and plan for a less mature operational knowledge base.
Final Thoughts: Choosing the Right Gateway API Strategy
In the first article in this series, we saw that Ingress solved an important problem, but many teams have reached the limits of what it was designed to handle.
Gateway API addresses those structural problems. But Gateway API is a contract, not an outcome.
The implementation you choose determines how that model behaves in practice—how much complexity you carry forward, how your teams collaborate, and how your platform evolves over time.
The goal isn’t just to move beyond Ingress—it’s to avoid carrying its hidden complexity into your next architecture.
For most of the platforms we’ve worked with, Envoy Gateway represents the most durable starting point: built around the spec, strong on security, governed openly, and with an extension model that’s designed to stay coherent as the ecosystem matures. That’s not a universal answer. But it’s where we’d start, and where we’ve seen teams find the most confidence on both day one and day two.